As cloud technologies become more mature, we are seeing a rapidly increasing number of organizations adopting a public or hybrid cloud strategy in their IT infrastructure. While cloud technologies offer virtually infinite computing capabilities, many organizations are still wary of the security limitations of public cloud environments. But, is this concern merely a speculation or based on actual facts? Perhaps a better question would be, “What kind of security capabilities does Alibaba Cloud offer?”
In this article, we will address these concerns by discussing the top 5 security considerations you should look out for in a cloud provider. The Alibaba Cloud Security team has also written a detailed security whitepaper, covering all your security concerns of deploying on Alibaba Cloud.
1. Security Architecture of Cloud Provider
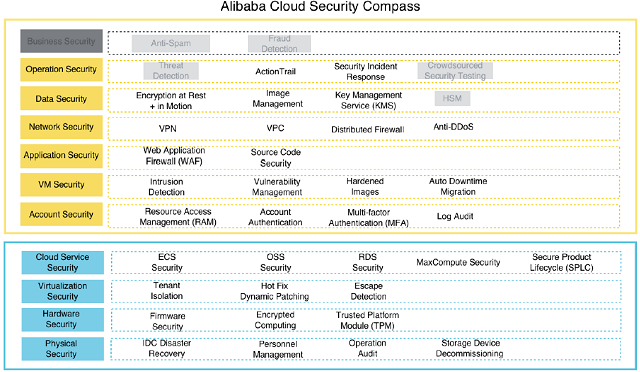
The security features of Alibaba Cloud are built on top of an 11-layer security architecture dubbed the "Security Compass". The Alibaba Cloud Security Compass consists of four layers oriented at cloud platform and seven layers oriented at cloud users. By abstracting cloud platform and user security, Alibaba Cloud allows users to focus on security at the implementation level, including account, VM, application, network, data, operation, and business security. Please note that there are several items being greyed out in the diagram below. The greyed-out items are the ones currently only available in Mainland China, though they would be made available globally in the future.
2. Security Features of Cloud Products
Obviously, one of the main considerations when it comes to ensuring security on the cloud is to make sure the products that you use are robust. This means that even without any additional security products and services, the cloud product of your choice must be able to withstand a variety of cyber-attacks.
Alibaba Cloud Elastic Compute Service (ECS) instances can achieve this by employing features such as tenant isolation. Tenant isolation is achieved by providing isolation between the virtual machine management (VMM) system and the customer's VM, and isolation between customer's VMs. On Alibaba Cloud, ECS instances that are assigned to different users are isolated, providing the needed security barriers among tenants.
Other security features of Alibaba Cloud products include security group firewalls, whitelisting, resource access management, and anti-IP/MAC/ARP spoofing.
3. Security Services Offered by Cloud Provider
Despite having all these security features, your IT infrastructure is still not completely immune to cyber-attacks. If you want to keep your data and applications secure, you should definitely consider investing in cyber security products offered by your cloud provider.
Alibaba Cloud suite of security products are built on Alibaba Group’s security technologies and experiences over the years. From its free services such as Server Guard Basic and Anti-DDoS Basic versions to value-added ones such as Anti-DDoS Pro, Alibaba Cloud provides a one-stop security solution for all types of businesses.
4. Security Compliance and Credentials
For users to operate freely across the globe, cloud providers need to adhere to domestic and international information security standards, as well as industry requirements. Cloud providers should integrate compliance requirements and standards into internal control frameworks, and implement such standards by design in their cloud platform and products.
Alibaba Cloud is actively involved in the development of multiple standards for the cloud industry, and is also engaged with multiple independent third parties to verify its compliance. Alibaba Cloud is certified by more than 10 agencies across the globe, and is a cloud service provider with the most complete range of certifications in Asia.
Visit the Alibaba Cloud Security and Compliance Center to see our list of certifications and compliance credentials.
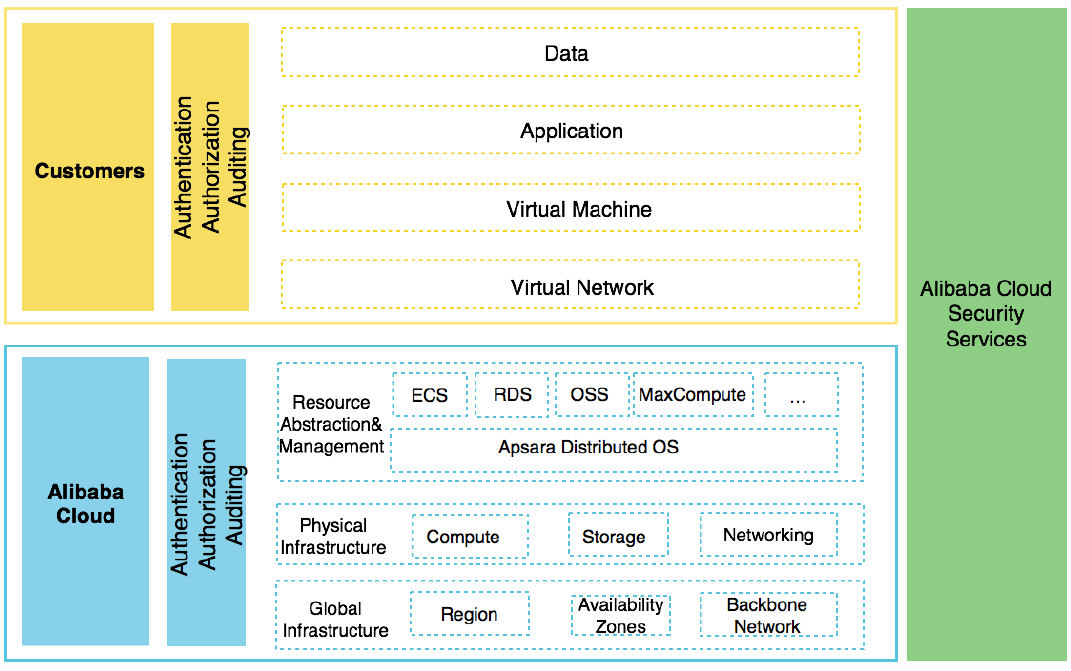
5. Shared Security Responsibility Model
Alibaba Cloud and its customers are jointly responsible for the security of customers' applications built on Alibaba Cloud. On Alibaba Cloud, customers are responsible only for the security of applications built on top of or connected to the cloud. Alibaba Cloud, on the other hand, is responsible for the security of the underlying cloud service platform and infrastructure. By maintaining this model, customers are able to leverage the underlying security assurance and capabilities that Alibaba Cloud provides. Additionally, customers can rest assured that they have full control over the security of their data.
About the Alibaba Cloud Security Whitepaper
The Alibaba Cloud Security Whitepaper provides a comprehensive guideline and description of the Alibaba Cloud's security architecture, which constructs the security foundation of the entire Alibaba Cloud platform.
Additionally, the Security Whitepaper includes detailed descriptions of key security features and capabilities of Alibaba Cloud products. Moreover, best practices are provided within the whitepaper for a number of products to help customers to use Alibaba Cloud more securely.
Data security and user privacy are the top priorities of Alibaba Cloud. Alibaba Cloud strives to provide customers with consistent, reliable, secure, and regulation-compliant cloud computing services, helping customers ensure the availability, confidentiality, and integrity of their systems and data.
Download the full whitepaper by visiting https://www.alibabacloud.com/help/faq-detail/42435.htm